Why Zero Trust Architecture Implementation Is No Longer Optional

In today’s digital landscape, cybersecurity threats have grown more sophisticated, more frequent, and far more damaging. Traditional perimeter-based security, which is built on the idea that everything inside a network can be trusted, simply can’t keep up. As hybrid work expands, cloud adoption accelerates, and federal cybersecurity guidance tightens, organizations can no longer rely on outdated security models to protect sensitive data.
Hence why Zero Trust architecture implementation is quickly shifting from an optional upgrade to a business and mission-critical necessity.
What Zero Trust Really Means (and Why It Matters)
Zero Trust is built on a simple, powerful principle: never trust, always verify. Instead of assuming internal users or devices are safe, Zero Trust verifies every interaction, every time, based on identity, behavior, device health, and context.
This modern approach dramatically reduces the attack surface and prevents intruders from moving laterally across a network, which is a major vulnerability in legacy security models.
For federal agencies, contractors, and technology-driven organizations, Zero Trust has become an operational imperative.
Why Zero Trust Architecture Implementation Can’t Wait
1. Cyber Threats Are Evolving Faster Than Traditional Defenses
Ransomware, credential theft, insider threats, and supply-chain attacks are increasing in frequency and complexity. Perimeter-based defenses leave too many gaps, especially as organizations adopt cloud environments, remote work setups, and distributed infrastructures.
Zero Trust limits damage by verifying identity and access at every point, ensuring even compromised credentials or devices don’t automatically gain broad access.
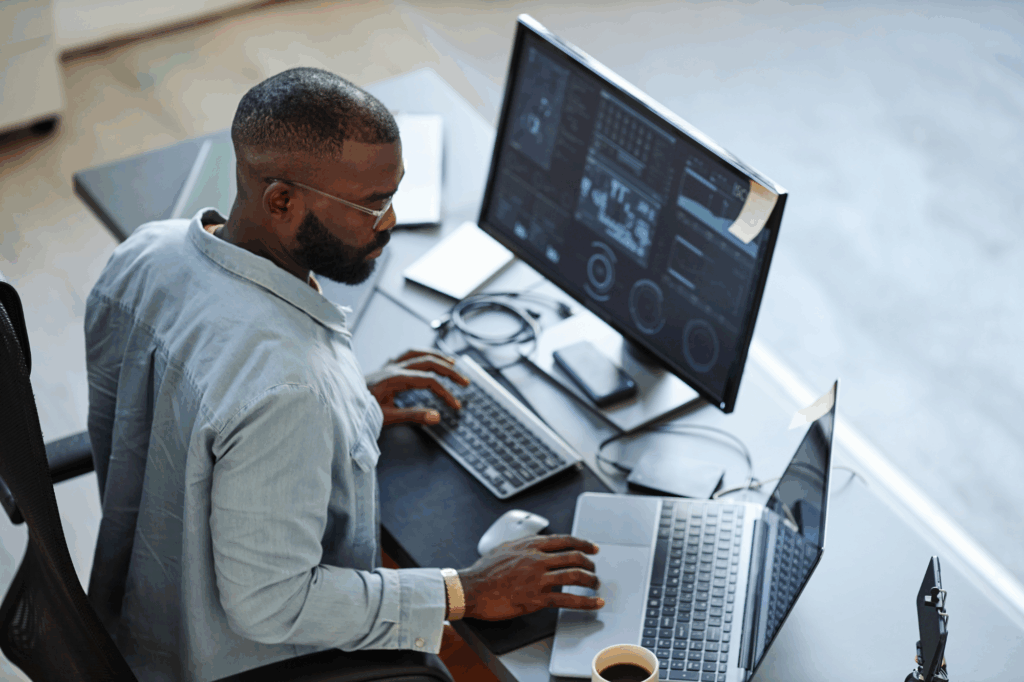
2. Hybrid and Remote Work Introduce New Attack Surfaces
As employees work from multiple locations and devices, networks become more open and vulnerable. Zero Trust ensures that access is based on continuous authentication, not physical location, making it far better suited to modern work.
3. Cloud Adoption Demands a Modern Security Model
Cloud environments operate differently from traditional data centers, and perimeter security simply doesn’t work in a cloud-first world. Zero Trust aligns security controls across multi-cloud, hybrid cloud, and on-prem environments, improving consistency and reducing risk.
4. Insider Threats Are More Common Than You Think
Insider security breaches are one of the most difficult risks to detect. Zero Trust mitigates this by limiting access, monitoring behavior, and ensuring users only access the resources required for their role.
5. The Cost of a Breach Is Too High to Ignore
Data breaches, downtime, loss of sensitive information, and reputational damage can cost organizations millions. Zero Trust doesn’t eliminate all risks, but it greatly reduces the likelihood and impact of security incidents, making it one of the highest-value investments organizations can make today.
Building an Effective Zero Trust Strategy Takes the Right Expertise
Zero Trust implementation is a complete shift in mindset, architecture, and ongoing operations. Successful adoption requires expertise across:
- Identity and access management (IAM)
- Network segmentation
- Continuous monitoring and analytics
- Cloud security engineering
- Endpoint protection
- Secure DevOps practices
- Federal compliance and cybersecurity standards
Because Zero Trust touches every part of an organization’s infrastructure, having the right team in place is essential.
Partnering with the Experts Matters
A tailored, strategic approach ensures Zero Trust is implemented correctly, efficiently, and in alignment with mission and business needs. That’s where the right technical talent makes all the difference.
Secure Your Future with Gridiron IT
Zero Trust architecture has become a foundational requirement for protecting your organization, supporting federal missions, and staying ahead of evolving threats.
Gridiron IT connects organizations with highly skilled cybersecurity, cloud, and IT professionals who understand Zero Trust and can help you build a stronger, more resilient security posture.
If you’re ready to advance your Zero Trust strategy, connect with Gridiron IT today and secure the trusted talent you need to protect what matters most.